Table of Contents
Hackers may have compromised the networks of thousands of businesses due to a supply-chain attack on the enterprise phone company 3CX, which confirmed on Thursday its desktop app had been bundled with malware.
3CX provides office phone systems to more than 12 million daily users at over 600,000 companies, as it claims on its website, including Mercedes-Benz, Coca-Cola and the United Kingdom's National Health Service.
The extent of the impact on these companies is not yet clear. The Record has contacted them for comment. A spokesperson for Mercedes-Benz declined to respond. American Express said that despite being listed on 3CX’s website they were not a client of the company and did not use 3CX’s software.
In a statement published on the company’s community forum Thursday morning, founder and chief executive Nick Galea confirmed that “the 3CX DesktopApp has a malware in it.”
Later Thursday, the company’s chief information security officer, Pierre Jourdan, said the intrusion was the work of highly skilled hackers.
Source: The Record (Recorded Future News)
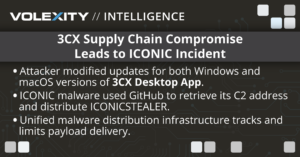
In a public post on Reddit, CrowdStrike identified signed 3CX installation files as being malicious and reported that customers were seeing malicious activity emanating from the “3CXDesktopApp”. Volexity further identified public forum postings on 3CX’s own website that stated various endpoint detection and response (EDR) and antivirus (AV) vendors began flagging malicious activity from updates as early as March 22, 2023. Volexity’s analysis suggests the malicious activity likely began much earlier.
Volexity was able to obtain multiple malicious installers for Windows and macOS directly from 3CX download servers. Analysis of installers from both platforms allowed Volexity to identify several new indicators of compromise and gain further insight into how the malware functions.
This post details what Volexity discovered from its analysis of the malicious installers and the additional files it downloads. Highlights of the findings include the following:
- Both the macOS and Windows installers for 3CX are affected.
- Based on data recovered from GitHub, infrastructure used by the Windows variant was activated on December 7, 2022.
- Domains and web infrastructure used in the attacks were registered as early as November 2022.
- A reconnaissance payload was deployed far and wide to Windows users.
- The same functionality to download a payload was identified in the macOS sample, although Volexity could not confirm the final payload as the C2 was unresponsive at the time of analysis.
Any endpoint impacted by this malicious update should be isolated and investigated for further signs of compromise. Organizations should assess the potentially impacted information on these endpoints and look to cycle secrets to reduce the risk of additional future compromise.
Some parts of malicious code identified in the analysis of the attacks could be linked to the North Korean hacker group Lazarus. ICONIC malware in compromised 3CX apps use Github to retrieve its C2 address and distribute ICONICSTEALER.
Infrastructure & Attribution
In terms of attacker infrastructure, the domains used in these attacks are hosted on shared infrastructure and appear to simply proxy requests to an unknown upstream C2. Domains were registered with several providers, including NameCheap, Public Domain Registry, and NameSilo. Some of the domains were not registered using WHOIS protection, and each was registered using a unique email address. The following emails were observed in WHOIS records for related domains:
- cliego.garcia@proton[.]me
- remey.simpson@outlook[.]com
- jackiewcaudill@gmail[.]com
- philip.je@proton[.]me
- haroldjmarable@gmail[.]com
In terms of attribution, the original CrowdStrike post suggests the incident is related to LABYRINTH CHOLLIMA, which is related to the public Lazarus moniker (although Volexity does not have visibility of exactly which parts of Lazarus this maps to). Volexity cannot currently map the disclosed activity to any threat actor, so it will be tracked under UTA0040.
Conclusion & Mitigations
Volexity’s analysis concludes that both the Windows and macOS installers for the 3CX desktop application had malicious code inserted into them before being provided to customers. This suggests that 3CX was itself compromised by the threat actor for a period of time prior to the infection, allowing the attacker to develop an understanding, access, and malicious code for the development-update process of the company.
The end result for victims of this campaign was that information-stealing malware was installed on endpoints that installed this update, and for selected victims, an additional arbitrary payload may also have been delivered.
Supply chain attacks are relatively rare due to the high level of technical and operational capability required for success. However, organizations with a large customer base, such as 3CX, are attractive targets due to the broad level of access these attacks can grant threat actors.
Volexity assesses that it is likely UTA0040 is a nation-state-backed threat actor based on the level of capabilities utilized in this campaign, combined with a perceived intent to gather information from victims for further targeted compromise. Crimeware-based threat groups who have historically conducted supply chain attacks typically push ransomware payloads immediately with their access, rather than try to conduct reconnaissance to filter victims of their true payload. While Volexity cannot attribute this cluster to any known group at this time, CrowdStrike has attributed this activity to LABYRINTH CHOLLIMA, a North Korean group.
Supply chain attacks are complex issues for defenders to defend against. This instance highlights how large code bases can be backdoored with minor additions to existing code and remain undetected by the software provider and the end user. However, information in the public domain highlights the value of endpoint and network detection capabilities, which provided valuable identification of anomalous behavior that may have prevented further impact for end users.
The infrastructure registration and public artifacts (notably the GitHub page) suggests that the attacker had access to the software provider at least as early December 2022, and perhaps as early as November 2022. It is not clear when the first malicious update described in this post was downloaded by victims of this campaign, but the public discussions around detections suggest this could be as early as March 22, 2023. This does not rule out other potentially malicious activities having occurred before this time related to this software.
To detect and investigate these attacks such as these, Volexity recommends the following:
- Use the YARA rules provided here to detect related activity.
- Use the provided Suricata rules here to detect related activity. It should be noted that these requests take place over HTTPs, meaning they are only effective if this traffic is being decrypted prior to matching.
- Block the IOCs provided here.
Appendix A – Third-Party Reporting
There is a great deal of third-party reporting on this subject covering various aspects of the campaign. A list of resources is provided below, note that this list was compiled on March 30, 2023, and inevitably more resources will become available after publication.
Social Media Posts
- https://twitter.com/cyb3rops/status/1641130326830333984 (https://github.com/SigmaHQ/sigma/pull/4151/files, https://github.com/Neo23x0/signature-base/blob/master/yara/gen_mal_3cx_compromise_mar23.yar)
- https://twitter.com/cyb3rops/status/1641339448053858304
- https://twitter.com/patrickwardle/status/1641294247877021696
- https://twitter.com/fr0gger_/status/1641325932760948737
- https://twitter.com/donnymaasland/status/1641349104113524736
- https://twitter.com/jamesspi/status/1641262032870686721
- https://twitter.com/dez_/status/1641204732445478912
- https://twitter.com/vxunderground/status/1641261800594210817
CrowdStrike
- https://www.crowdstrike.com/blog/crowdstrike-detects-and-prevents-active-intrusion-campaign-targeting-3cxdesktopapp-customers/
- https://www.reddit.com/r/crowdstrike/comments/125r3uu/20230329_situational_awareness_crowdstrike/
Sophos
SentinelOne
Symantec
3CX
Objective-See
Bleeping Computer
Huntress
Other related sources
#SupplyChain #CyberAttack #Campaign #IoCs #VoIP










